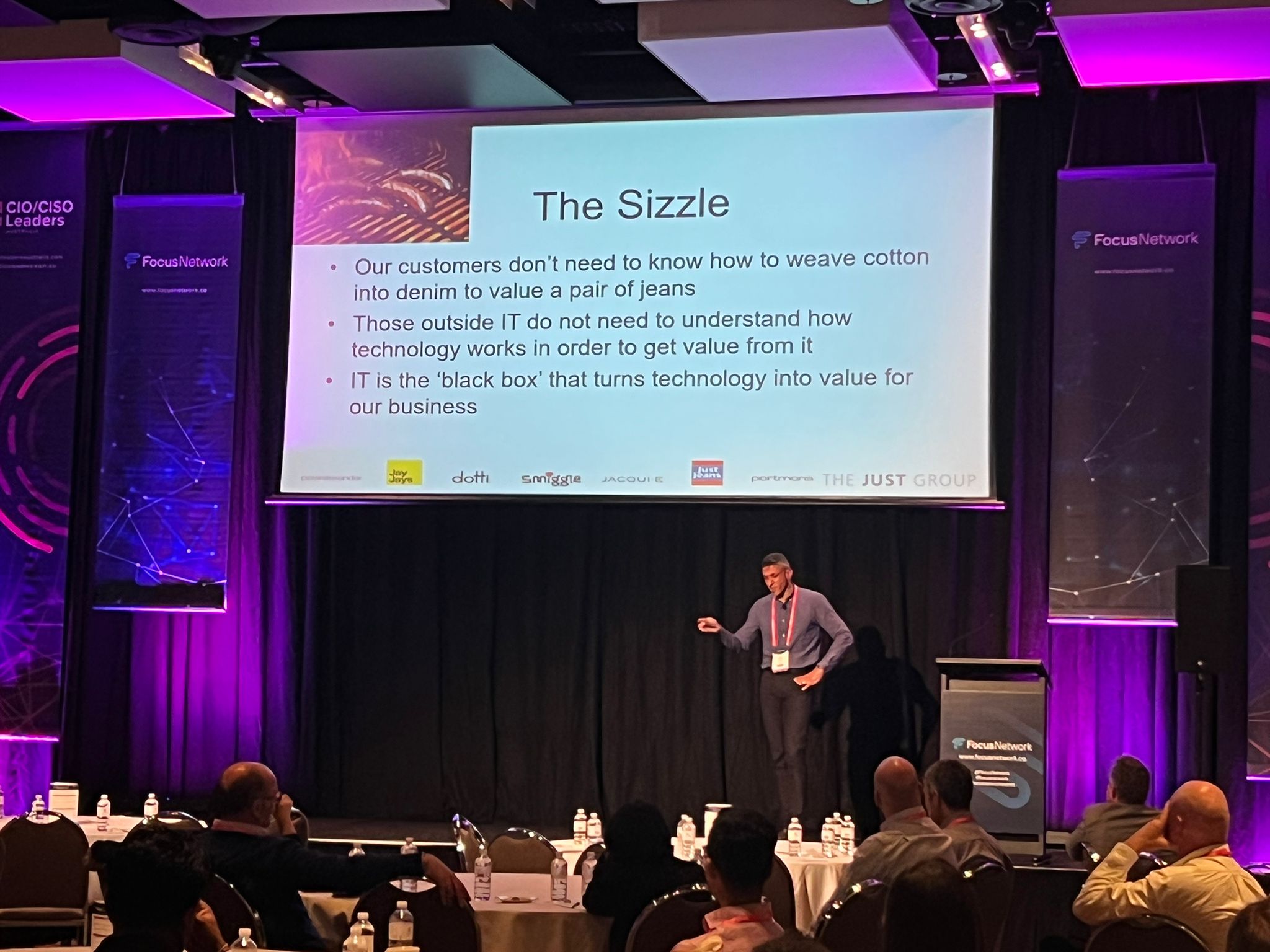
Frank De Sa, Chief Information Officer, Just Group Limited
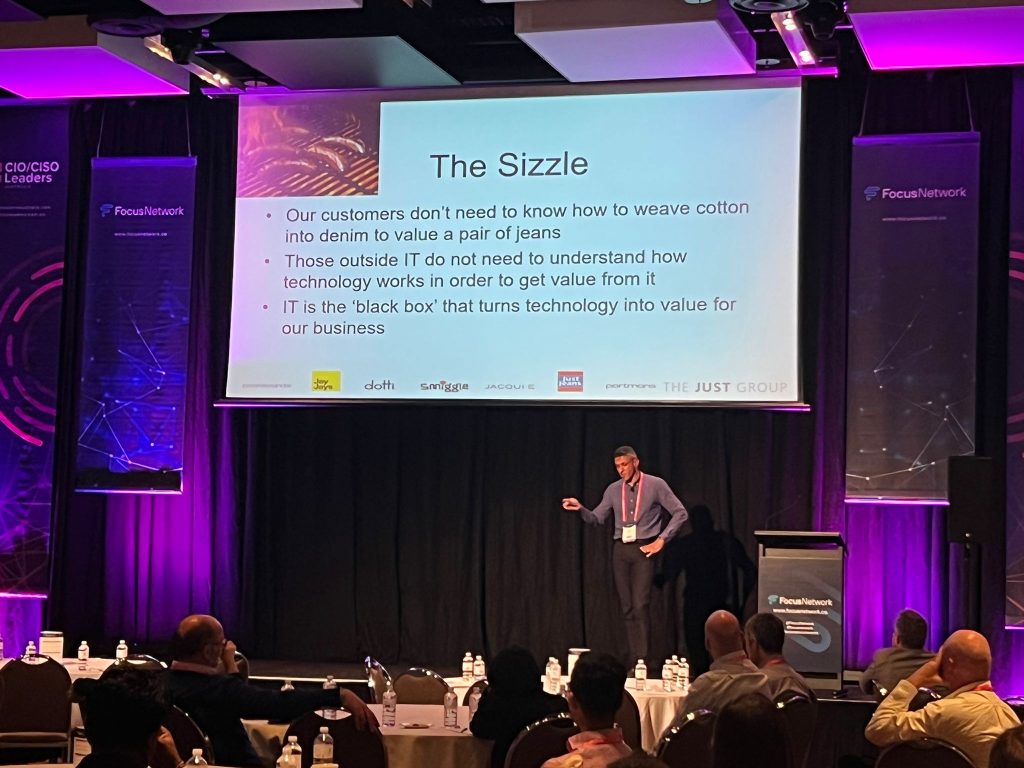
The presentation was based around “Attitude, Language & Approach – Keys to CIO Success”, and delved into:
- Technology has evolved from the domain of the geeky to the domain of everyone!
- Have IT Departments really understood and embraced this fundamental shift?
- Are vendors, marketers, and researchers controlling our destiny or do we use them strategically as inputs into decision processes for our businesses?
- Why is IT/Business Alignment still on the agenda? Why is our language and attitude critically important to our success? Why do we still refer to ‘the business’ as ‘the business’ vs IT?
- Is digital transformation simply the latest buzzword to sell more software and services or does it have meaning within IT departments?